Learn Engineering
- operating system
- software engineering
- artifical ntelligence
- C++
- computer network
- programming language
- theory of automata
- analysis and design of algo
- computer graphics
- dbms
- java
- microprocessor
- multimedia technologies
- web development
- system programming and administrator
- Computer architecture and organization
Monday, 5 February 2018
Saturday, 3 February 2018
Monday, 22 January 2018
Beware! These “Forced” Chrome And Firefox Extensions Are Almost Impossible To Remove

Google Chrome is often labeled as one of the best web browsers around for all the right reasons. Players like Firefox are competing by adding innovative features, but Chrome continues to enjoy an unparalleled popularity. However, this doesn’t mean that Chrome is 100% secure. A security researcher has spotted malicious add-ons that’s almost impossible to delete.
These extensions have been spotted in both Mozilla Firefox and Google Chrome. They use techniques to redirect users away from pages where they can remove the extensions and try to hijack traffic for driving clicks on other web pages.
Chrome and Firefox both are affected
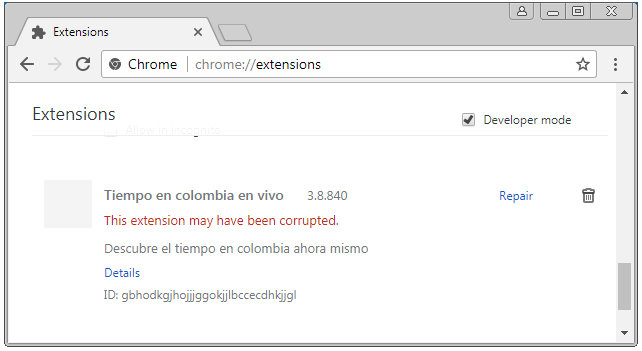
For Chrome, the researcher found an extension named Tiempo en colombia en vivo. It gets pushed via a method called “Forced Chrome Extension.”To drive away users from the extensions page, it redirects the uses from chrome://extensions/ to chrome://apps/?r=extensions. On this page, only installed apps are listed. Blocking JS in Chrome or starting Chrome with disabled extensions doesn’t help as well.
A method to stop the extensions from operating is by renaming the 1499654451774.js file in the extensions folder. It shows up in the extensions list as corrupted.
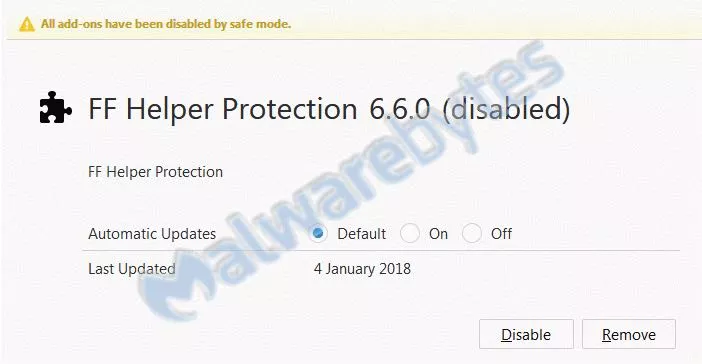
Malwarebytes also found a similar extension in Firefox with name PUP.Optional.FFHelperProtection. It blocks about:addons in background.js and prohibits the user from removing it.
Removal in Firefox is comparatively easier as one can see all the installed extensions by running the browser in safe mode.
While the exact extensions might not exist on the online stores at the moment, their modified versions continue to prevail. As they arrive on the machines of users via forced installs, it’s difficult to avoid them every single time. So, the users are advised to surf the web with caution and use recommended security methods. Before downloading extensions, users should also read their descriptions and reviews carefully.
It’s also worth noting that these extensions highlight a picture that involves Google’s failure to ensure proper scrutiny when it comes to Play Store or Chrome Store. So, unless Google makes its review process for third-party extensions and apps more stringent, such problems aren’t going to go away.
Saturday, 20 January 2018
15-Year-Old Schoolboy Posed as CIA Chief to Hack Highly Sensitive Information

A
notorious pro-Palestinian hacking group behind a series of embarrassing
hacks against United States intelligence officials and leaked the
personal details of 20,000 FBI agents, 9,000 Department of Homeland Security officers, and some number of DoJ staffers in 2015.
Believe or not, the leader of this hacking group was just 15-years-old when he used "social engineering" to impersonate CIA director and unauthorisedly access highly sensitive information from his Leicestershire home, revealed during a court hearing on Tuesday.
Kane Gamble, now 18-year-old, the British teenager hacker targeted then CIA director John Brennan, Director of National Intelligence James Clapper, Secretary of Homeland Security Jeh Johnson, FBI deputy director Mark Giuliano, as well as other senior FBI figures.
Believe or not, the leader of this hacking group was just 15-years-old when he used "social engineering" to impersonate CIA director and unauthorisedly access highly sensitive information from his Leicestershire home, revealed during a court hearing on Tuesday.
Kane Gamble, now 18-year-old, the British teenager hacker targeted then CIA director John Brennan, Director of National Intelligence James Clapper, Secretary of Homeland Security Jeh Johnson, FBI deputy director Mark Giuliano, as well as other senior FBI figures.
Between June 2015 and February 2016, Gamble posed as Brennan and tricked call centre and helpline staff into giving away broadband and cable passwords, using which the team also gained access to plans for intelligence operations in Afghanistan and Iran.
The teenager also taunted his victims and their families, released their personal details, bombarded them with calls and messages, downloaded and installed pornography onto their computers and took control of their iPads and TV screens.
He also made hoax calls to Brennan's home and took control of his wife’s iPad.
At one point, Gamble also sent DHS secretary Johnson a photograph of his daughter and said he would f*** her, phoned his wife, leaving a voicemail message which said: "Hi Spooky, am I scaring you?," and even managed to get the message "I own you" on the couple's home television.
Gamble was arrested in February 2016 at his council home in Coalville and last October he pleaded guilty to 8 charges of "performing a function with intent to secure unauthorised access" and 2 charges of "unauthorised modification of computer material."
Gamble's defence said he was technically gifted but emotionally immature and has an autistic spectrum disorder, at the time of his offending, he had the mental development of a 12 or 13-year-old.
Also, the defence said, at no point did Gamble attempt to profit from his actions.
Out of 10 counts, Gamble previously admitted 8 charges of performing a function with intent to secure unauthorised access.
The teenager will be sentenced when the hearing resumes at a later date.
Two other members of Crackas With Attitude hacking group, Andrew Otto Boggs and Justin Gray Liverman, were arrested by FBI in September 2016 and had already been sentenced to five years in federal prison.
Friday, 19 January 2018
Facebook Password Stealing Apps Found on Android Play Store

Even after many efforts made by Google last year, malicious apps always somehow manage to make their ways into Google app store.
Security researchers have now discovered a new piece of malware, dubbed GhostTeam, in at least 56 applications on Google Play Store that is designed to steal Facebook login credentials and aggressively display pop-up advertisements to users.
Discovered independently by two cyber security firms, Trend Micro and Avast, the malicious apps disguise as various utility (such as the flashlight, QR code scanner, and compass), performance-boosting (like file-transfer and cleaner), entertainment, lifestyle and video downloader apps.
Like most malware apps, these Android apps themselves don’t contain any
malicious code, which is why they managed to end up on Google's official
Play Store.
Once installed, it first confirms if the device is not an emulator or a virtual environment and then accordingly downloads the malware payload, which prompts the victim to approve device administrator permissions to gain persistence on the device.

How Android Malware Steals Your Facebook Account Password
As soon as users open their Facebook app, the malware immediately prompts them to re-verify their account by logging into Facebook. Instead of exploiting any system or application vulnerabilities, the malware uses a classic phishing scheme in order to get the job done.
These fake apps simply launch a WebView component with Facebook look-alike login page and ask users to log-in. Apparently, WebView code steals the victim's Facebook username and password and sends them to a remote hacker-controlled server.
"This is most likely due to developers using embedded web browsers (WebView, WebChromeClient) in their apps, instead of opening the webpage in a browser," Avast said.
Trend Micro researchers warn that these stolen Facebook credentials can later be repurposed to deliver "far more damaging malware" or "amass a zombie social media army" to spread fake news or generate cryptocurrency-mining malware.
Stolen Facebook accounts can also expose "a wealth of other financial and personally identifiable information," which can then be sold in the underground markets.
Security firms believe that GhostTeam has been developed and uploaded to the Play Store by a Vietnamese developer due to considerable use of Vietnamese language in the code.
According to the researchers, the most users affected by the GhostTeam malware reportedly resides in India, Indonesia, Brazil, Vietnam, and the Philippines.
Besides stealing Facebook credentials, the GhostTeam malware also displays pop up adverts aggressively by always keeping the infected device awake by showing unwanted ads in the background.

Play Protect security feature uses machine learning and app usage analysis to remove (i.e. uninstall) malicious apps from users Android smartphones in an effort to prevent any further harm.
Although malicious apps floating on the official app store is a never-ending concern, the best way to protect yourself is always to be vigilant when downloading apps, and always verify app permissions and reviews before you download one.
Moreover, you are strongly advised to keep a good antivirus app on your mobile device that can detect and block such threat before they infect your device, and most importantly, always keep your device and apps up-to-date.
Wednesday, 17 January 2018
How To Get Android One Launcher With Google Feed On Your Phone (No Root Required)

Android One devices are Google’s attempt at providing a better experience for Android users purchasing budget devices. Just like the Pixel devices, there is a custom launcher app available for Android One.
While it is designed to work on these devices, determined developers are always in search of ways to bring them to other Android smartphones. Moving ahead on similar lines, the Android developer Amir Zaidi (AmirZ) has managed to develop a port of the Android One launcher present on Xiaomi A1 smartphone.
In September last year, AmirZ released a port of the Google Pixel Launcher that came to Google-made devices with Android 8.0 Oreo. His work inspired other Android launchers to add support for Google Now feed. It was followed by the release of the modded version of the Google Pixel 2 launcher by XDA member paphonb, featuring the Google Search bar at the bottom.
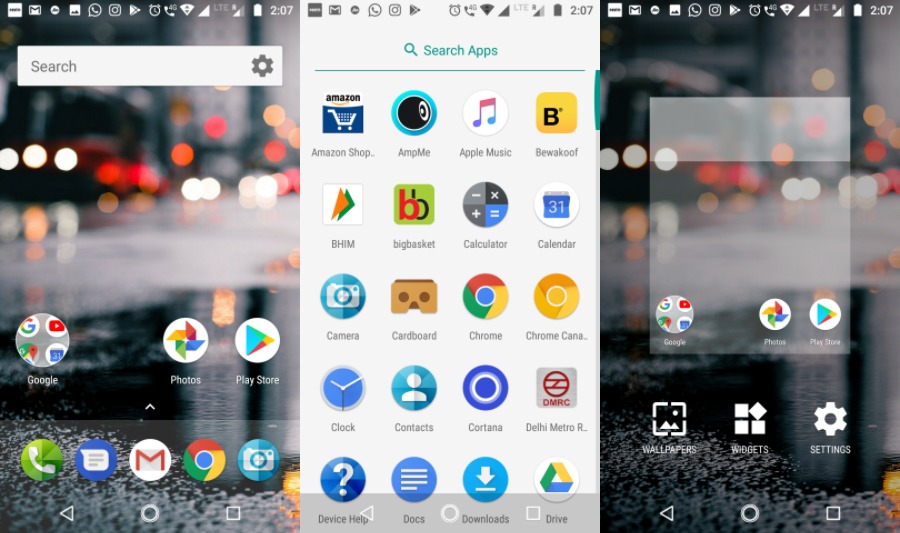
AmirZ’s Android One launcher can be easily sideloaded as it doesn’t require the device to be rooted. Also, it comes with a working Google Now Feed. When compared to the Google Pixel launcher, it has some visual distinctions. The app drawer has a white background.
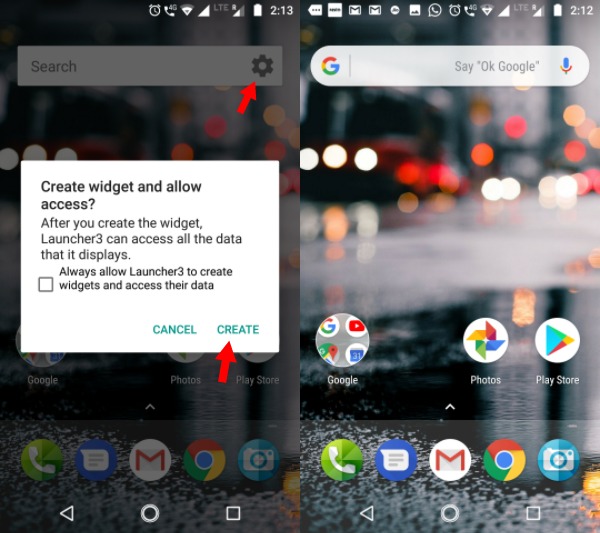 |
|There is one small twist, the rectangle Google search bar on the home screen turns into the rounded one we see on Pixel devices. Just tap on the small gear button and agree to the prompt displayed.
You can download the Android One launcher using this link.
Using BitTorrent For Downloading? This Security Flaw Lets Hackers Control Your PC Remotely
Even though the popularity of streaming websites is rising at a fast pace, BitTorrent remains a premier source of entertainment content source for a large chunk of people using the web. With the help of tons of popular torrent sites (there are some completely legal ones as well) and BitTorrent clients, people download content.
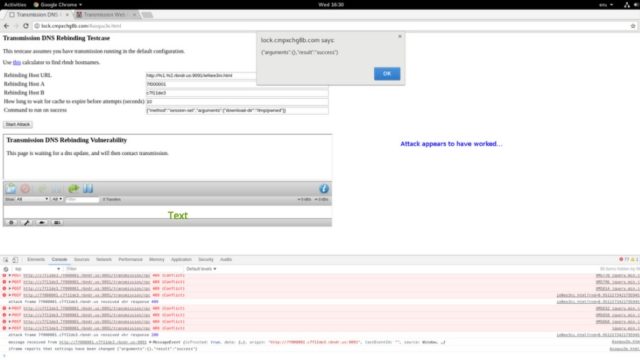
A recent critical vulnerability spotted by Google’s Project Zero team targets the popular Transmission BitTorrent app. By exploiting this flaw, a hacker can execute malicious code on the users’ computer, according to Ars Technica.
Last week, the Project Zero researchers published the proof-of-concept attack code. It’s worth noting that Project Zero normally refrains itself from making the details of such flaws public for 90 days or until the fix is released. However, in this case, the flaw was made public only 40 days after the initial report. This happened because the report included a patch to fix the vulnerability but Transmission developers didn’t respond on their private security mailing list.
After the public release of the flaw, the downstream projects using the Transmission project would be able to inculcate the patch in their implementations.
With the help of a hacking technique called domain name system rebinding, this exploit can control the Transmission interface when the target visits a malicious website. This can be further made easier by creating a DNS name which attacker is authorized to communicate with.
After controlling the Transmission interface, the attacker needs to change the torrent download directory to home and download a torrent named .bashrc. The attacker can also configure Transmission to run any command after the download has completed.
The Transmission developers have promised to release the fix as soon as possible. However, no specific date was given.
Subscribe to:
Comments (Atom)
operating system quick guide
Operating System - Overview An Operating System (OS) is an interface between a computer user and computer hardware. An operating system ...
-
ER Model, when conceptualized into diagrams, gives a good overview of entity-relationship, which is easier to understand. ER diagrams can ...
-
For a huge database structure, it can be almost next to impossible to search all the index values through all its level and then reach the...
-
DBMS stands for D ata b ase M anagement S ystem. We can break it like this DBMS = Database + Management System. Database is a collection ...
-
Crash Recovery DBMS is a highly complex system with hundreds of transactions being executed every second. The durability and robustness ...